14 JUNE: WORLD BLOOD DONOR DAY is celebrated every year on this day to raise awareness about safe blood donations and to thank those who donate blood voluntary and save the lives of others.
On June 14, Nobel prize winner and scientist Karl Landsteiner was born. He has got the credit for finding the ABO blood group system. World Blood Donor Day is celebrated on the birthday of Karl Landsteiner,who discovered various blood groups.Before Carl detected blood groups, blood transfusions used to happen without knowing the various blood groups. This discovery made Karl Landsteiner win the Nobel Prize in the year 1930.
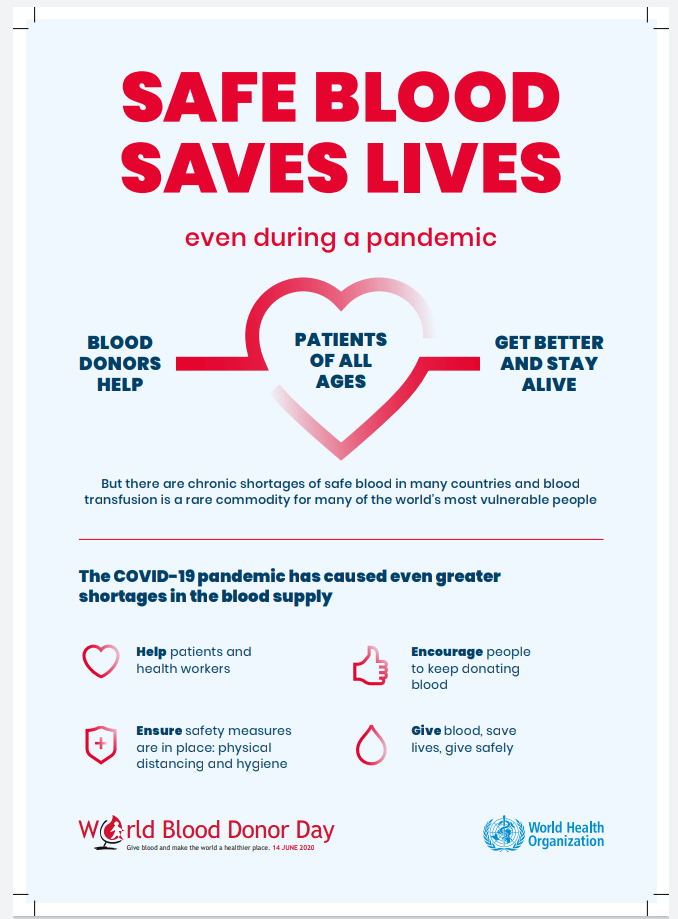
The theme for this year’s World Blood Donor Day is “Safe blood saves lives”with the slogan “Give blood and make the world a healthier place”. Every year, a host country is chosen to celebrate the National Blood Donation Day. Due to the Coronavirus outbreak, the WHO will conduct a global virtual campaign this year. The idea is to focus on the contribution an individual giver can make to improve health for others in the community.
Blood donation is voluntary, a noble deed and a great service which we can do for our fellow human beings. One donation of blood can save up to 5 lives. Blood transfusion helps patients in recovery and surgery, those who have platelet requirement, who have Hemophilia and ones undergoing organ transplantation or chemotherapy.
Benefits of donating blood:
- Helps in controlling weight.
- It keeps your liver healthy.
- Keeps cancer away.
- Helps in smooth blood circulation.
- Helps in burning calories.
Blood donation has been compounded severely by the Covid-19 pandemic and lockdown.In early April, the Indian Red Cross Society had raised an alarm that voluntary donation had fallen by almost 100%.This isn’t surprising, given that the number of Covid cases is rising, making infected people and those who come into contact with them ineligible to donate.
The Ministry of Health and Family Welfare has now issued guidelines for safe donation of blood during the ongoing pandemic. Go through the guidelines on this website to know safe blood donation during covid pandemic-https://www.mohfw.gov.in › …PDF
Web results
Advisory for Voluntary Blood Donation during COVID – MoHFW
The objectives of this year’s campaign are to:
- celebrate and thank individuals who donate blood and encourage more people to start donating.
- raise wider awareness of the urgent need to increase the availability of safe blood for use wherever and whenever it is needed to save life.
- demonstrate the need for universal access to safe blood transfusion.
- mobilize support at national, regional and global levels among governments and development partners to invest in.
For information on blood donation,visit-nbtc.naco.gov.in › faq
FAQs on Blood Donation – National Blood Transfusion Council (NBTC) – MoHFW …
The event serves to thank voluntary, unpaid blood donors for their life-saving gift of blood and also to raise awareness of the need for regular blood donations to ensure that all individuals and communities have access to affordable and timely supplies of safe and quality-assured blood and blood products, as an integral part of universal health coverage and a key component of effective health systems,” the WHO states.
All blood types can donate blood and they can do it whenever required.“Spare only 15 minutes and save one life”.